It is not uncommon to go from day to day and not think about an IT security audit. After all, the general human view is “if it isn’t broken, don’t fix it”. However, your IT in your company may be broken and you may not even know it. What happens next when hackers sneak through the back door of your computer system is something you never want to deal with.
You should know the ins and outs of an IT security assessment/audit and why they are so vital to your company. That should be your first step towards recognizing that your company needs an audit/assessment soon.
The Bigger the Target, the More Likely the Attack
Hackers and techno-terrorists rarely go after businesses that are only operated by less than five people. The money and the payout just aren’t there. What they want is to squeeze big companies into giving them a king’s ransom to release the companies’ IT departments.
The bigger the company is, the more likely it will come under attack. This includes some non-profits and public organizations that process thousands of files of data and millions of dollars annually. If a hacker thinks there is even the slightest chance of getting rich or mining enough data to resell on the Dark Web, he or she will do it.
Patient or Customer Information Is Worth More Than Gold
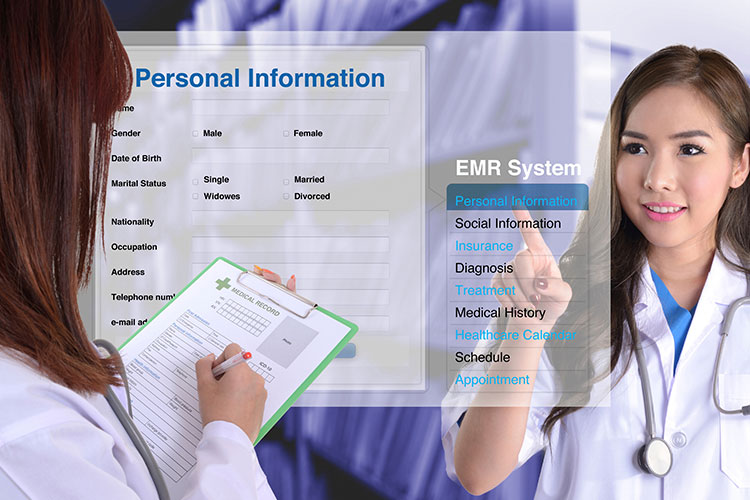
Another reason why hackers salivate at the chance to attack is because your company or business handles millions of transactions with customer or patient personal information. Social security numbers, passwords, addresses, telephone numbers and more are all key to hackers getting a big payday.
This kind of information can be sold for millions of dollars on the Dark Web if enough information is mined from your computer system. Buyers on the Dark Web use the data they buy from hackers to steal identities and set up fake accounts to steal even more money. Don’t let the source of financial ruin for clients or patients be your IT department.
Your Firewall Isn’t Enough
Hospitals and military bases may use firewalls on their computer systems, but the truth is that a hacker that is particularly good at navigating around or through firewalls isn’t going to be stopped. It may just take longer for him or her to break through.
If you are not performing frequent and adequate audits of your hardware and software applications, you are leaving your company exposed to a lot of risk and major losses. Hospitals that are attacked by hackers using ransomware often lose millions of dollars in operations costs and lawsuits by patients when the entire hospital comes under technical siege.
You can prevent that with first hiring really good IT people who know how to prevent these attacks. Then hire IT auditors who can stop the attacks from happening once the hackers have already made their way into the system. If it gets so far as a hacker making a demand for payment, an auditor can figure out how to shut down and shut out the hacker without losing data.
Your Computer Savvy Cousin Isn’t Enough Either

Hiring somebody to fill an IT position with your company should be more than just hiring somebody that knows things about computers and navigating back doors into your system. It should be more than somebody who can reboot and troubleshoot your computer too.
Don’t hire someone simply because they have a degree in IT management. Hire an IT security audit specialist or company that is extremely knowledgeable and has a ton of experience with audits and hacker prevention. Hire someone who knows how to look for code that hackers use to get in and out of your computer system undetected. That’s the person who can find out if hackers have entered your system and stolen anything of value.
Compliance with Cybersecurity Laws
There are laws and regulations in place to protect both businesses and consumers from cybercrimes. However, if you are not in compliance with the requirements stated in said laws and regulations, you could be charged with criminal negligence and could have a criminal records in sites like lookupinmate.
First and foremost, become familiar with what these cybersecurity laws expect you to do. Then hire the right company or person to handle your audits and risk assessments. The assessor/auditor can tell you right away what you are doing wrong and what you need to do to be compliant. You will be expected to make those changes to protect your company and your consumers or face penalties.
Risks You May Not Even Know Are Risks

The law does not accept ignorance as an excuse for crime. This also applies to cybercrime. Understanding what risks your company’s IT department is facing will help you understand what is at stake.
For example, setting up a new computer system or setting up a new computer to add to an existing system is a risk. It becomes a risk the minute you fail to install all of the right protocols and preventive measures and have the entire system checked for “open cyber-doors”. Your tech person has to make sure that all the computers and the entire system are extremely safe and well-protected.
Additionally, you need disaster recovery programs to protect company data. An excellent disaster recovery program stores vital information and data out of reach of a hacker.
If your system should still come under attack in the future, or a natural disaster damages vital computers, the recovery system can reboot all saved data on other computers connected to your system. The downside is that there’s a risk involved and the risk is ensuring proper protection.
Another risk is working remotely and using a personal laptop or computer to connect to the work system. A hacker can use your personal computer to get to the company computer, and then you really have problems. During an audit, the assessor/auditor can find out how many personal computers link to the work system and how many of those computers put your company’s system in danger.

